Critical infrastructure safeguards our way of life – it enables economic growth, communication, health, longevity, and public safety. There are many types of infrastructure that are vital to how we live. From the roads we drive on to the facilities and equipment that provide us with basic utilities, the lack of, or destruction of this infrastructure could threaten Americans’ livelihood, health, and safety. The United States government works to maintain, protect, and strengthen critical infrastructure by coordinating and partnering with private companies to adopt security requirements and policy that protect this infrastructure.
What Is Critical Infrastructure?
An infrastructure security plan is essential for promoting a more resilient nation. Identifying the networks, utilities, and facilities our society depends on is the first step to creating a strategy to reduce vulnerabilities and respond in the case of a disaster.
The Cybersecurity & Infrastructure Security Agency (CISA) spearheads the movement to identify the infrastructure – both physical and digital – that our society relies on. And the CISA works in hand with the Department of Homeland Security and other key government departments to create strategies and policies to strengthen and protect this infrastructure.
CISA has identified 16 sectors that are designated critical infrastructure and whose “incapacitation of destruction would have a debilitating effect on security, national economic security, national public health or safety, or any other combination thereof.”
These sectors include:
- Chemical Sector
- Commercial Facilities Sector
- Communications Sector
- Critical Manufacturing Sector
- Dams Sector
- Defense Industrial Base Sector
- Emergency Services Sector
- Energy Sector
- Financial Services Sector
- Food and Agriculture Sector
- Government Facilities Sector
- Healthcare and Public Health Sector
- Information Technology Sector
- Nuclear Reactors, Materials, and Waste Sector
- Transportation Systems Sector
- Water and Wastewater Systems Sector
The Communications Sector: The Core of All Critical Infrastructure
The communications sector has a rippling effect on all other critical infrastructure sectors. Without the ability to communicate and connect, many key aspects of society would fail. Businesses, individuals, and government agencies all depend on telecommunication infrastructure to maintain public safety and economic stability.
Over time, the communications sector has become more diverse. It now includes infrastructure such as subsea fiber optic cables, satellites and ground stations, utility poles, microwave transmitters, broadcasting equipment, data centers, and wireless networks. Private businesses provide most telecommunications infrastructure and services in the United States. As such, it is primarily up to these businesses to ensure these systems are reliable and secure.
Identifying Gaps and Vulnerabilities in Telecommunications
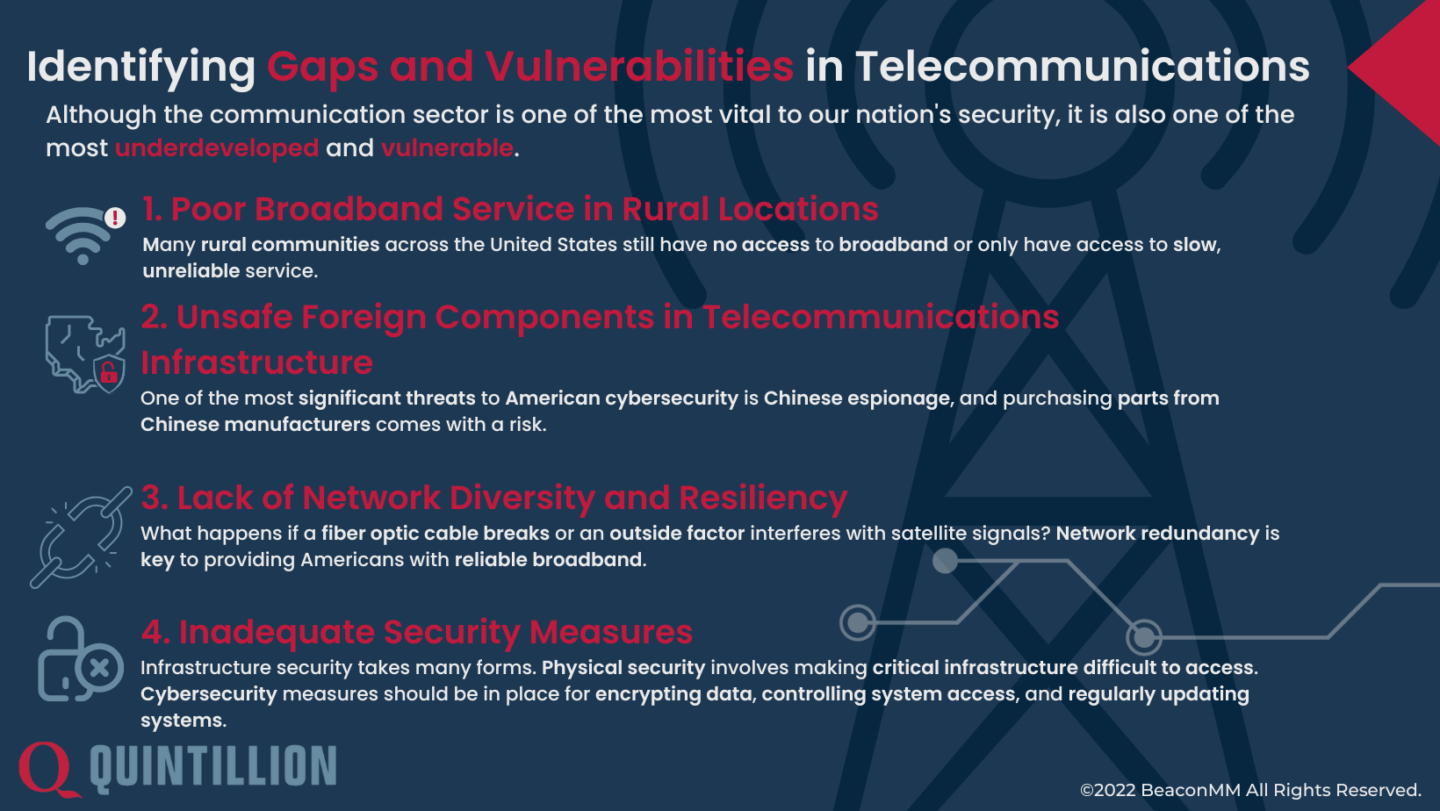
Although the communication sector is one of the most vital to our nation’s security, it is also one of the most underdeveloped and vulnerable. Throughout the nation, there are gaps in connectivity. There are certain regions where communication infrastructure is unavailable, unreliable, and/or unprotected. To strengthen our communication infrastructure security, we must continue to close the Digital Divide improve and secure existing infrastructure, network, and systems.
Closing the Digital Divide
While most major cities have access to high-speed, redundant, reliable internet service, many rural communities across the United States have no access to broadband or only have access to slow, unreliable service. Communities that lack broadband are majorly disadvantaged. This has significant negative impacts for businesses, education opportunities, and healthcare, as well as National Security.
Businesses are unable to compete in the Online marketplace and are unable to access essential services, including training or support that are now moving exclusively online. Hastened by the advent of Covid, many educational opportunities are online. This is true across the board from school age children through corporate trainings. Many healthcare providers now require electronic records and online consultations with doctors and nurses, which are surprisingly unavailable to many rural communities.
Gaps in connectivity also create blindspots in national security. For example, while the US Arctic is a highly contested space from a geopolitical standpoint, poor access to broadband infrastructure makes the United States vulnerable to its adversaries in this region. Improving communication in the Arctic enhances the military’s ability to defend the homeland and stay a step ahead of unpredictable threats.
Unsafe Foreign Components in Telecommunications Infrastructure
The components used to create satellites, routers, subsea cables, microwave towers, etc., matter. One of the most significant threats to American cybersecurity is espionage. The government has stringent rules in place that dictate where components may be manufactured and purchased from to ensure the safety of critical infrastructure.
A number of foreign manufacturers are prevented from supplying components or systems that will be used in critical Telecommunications Infrastructure. Of specific concern are a number of Chinese companies including Huawei Technologies and ZTE Corporation. Although products manufacturer by these corporations are often more affordable and widely available, these manufacturers, in concert with the Chinese government, may use this telecommunications equipment to spy, steal data from, or degrade infrastructure.
Lack of Network Diversity and Resiliency
What happens if a fiber optic cable breaks or an outside factor interferes with satellite signals? Network redundancy is key to providing Americans with reliable broadband. Network redundancy is when a network design duplicates telecommunication infrastructure to provide an alternate route in case of a network failure or disruption.
If a network lacks resiliency and redundancy, data only has one route to travel down. If anything disrupts the data’s path, it will have no way to reach its end location, and end users will lose internet service.
Inadequate Security Measures
Infrastructure security takes many forms. Physical security involves making critical infrastructure difficult to access. For instance, cable landing stations may be guarded, remotely monitored, or only accessible to approved individuals. These stations may be in hard-to-access locations and require several points of entry to get inside. The cables themselves should be resilient, buried when possible, and strategically routed to reduce the chance of harm. Additionally, cybersecurity measures should be in place, such as encrypting data, controlling system access, monitoring vulnerabilities, and regularly updating systems.
Quintillion’s Dedication to Critical Infrastructure Security
Quintillion’s critical fiber optic infrastructure is the only subsea and terrestrial fiber optic network in the North American Arctic. It provides Alaskans in this region with vital access to high-speed internet, opening job opportunities, enabling virtual health appointments, improving disaster response measures, and allowing for a wide range of digital communication tools. This infrastructure is also valuable to the US military in the Arctic, enabling enhanced communication among service members and paving the way for improved warning systems.
Quintillion also actively maintains a National Security Agreement with the United States government, which requires us to conform to certain infrastructure security requirements and standards. Additionally, we take stringent security measures to protect our equipment and the data of everyone who utilizes our networks and systems. Our infrastructure security protocol includes:
- Screening all personnel
- Least Privilege access to infrastructure
- Encrypting all data we process
- Constructing resilient fiber optic cables buried 12’ under ground
- Monitoring all equipment and facilities 24/7
- Utilizing redundant power sources to prevent outages
- Guarding and gating cable landing stations
- Constructing cable landing stations in remote, inaccessible areas
Additionally, our system does not include any non-compliant foreign components.
We take the security of our infrastructure seriously – from the planning phase to execution to maintenance, we’ve gone the extra mile to design our system to withstand Arctic conditions and resist any adversary parties attempting to infiltrate it.
Want to learn more about Quintillion’s dedication to communication resiliency in the Arctic and beyond? Contact our team to get in touch or read the Quintillion blog stay on top of the latest industry news.


